Your PC Isn’t Slow, It’s Mismanaged
- Your computer being sluggish isn’t necessarily down to the actual components inside.
- More often than not, systems are running poorly because they’re doing things with their power in a not-very-smart order.
- Apps running in the background, programs starting up automatically with Windows and processes you don’t even realize are happening all steadily use up your computer’s processing power and memory.
- This leads to delays when you do something, a struggle to have many things open at once and the computer simply not feeling as quick to react to you.
Improving your computer’s speed is about managing how it shares its abilities and isn’t just a matter of getting new hardware.
Understanding Performance Optimization
Optimizing your PC is about balancing:
- Speed
- Memory Usage
- Power Consumption
Every improvement comes with trade-offs:
- Faster performance may use more memory
- Lower power usage may reduce speed
Common issues:
- Too many apps running at once
- Too many browser tabs
- Background processes consuming resources
Real optimization means prioritizing what matters most for your workflow.
Why RAM Still Matters
- Right now, RAM is in charge of all the things your computer is doing.
- The more you ask it to do at once, the more RAM you’ll need.
- If you have more RAM, you’ll be able to do lots of things at the same time with no slowdown, switch between programs quickly and your computer generally will feel much more lively.
- However, you should always find out the most RAM your computer is designed to handle. Adding more RAM is good, but it won’t work if you exceed that limit.
And RAM is useful, but it won’t fix it if programs aren’t using the computer’s power efficiently.
The Real Problem: Background Apps Stealing Performance
- Many apps run silently in the background
- They Consume: CPU, memory & system priority
- Common culprits: Startup programs, Auto-launch apps & Idle background processes
- Impact: Slower boot times, Reduced system speed & Lag during important tasks
Your PC slows down because the wrong apps get priority.
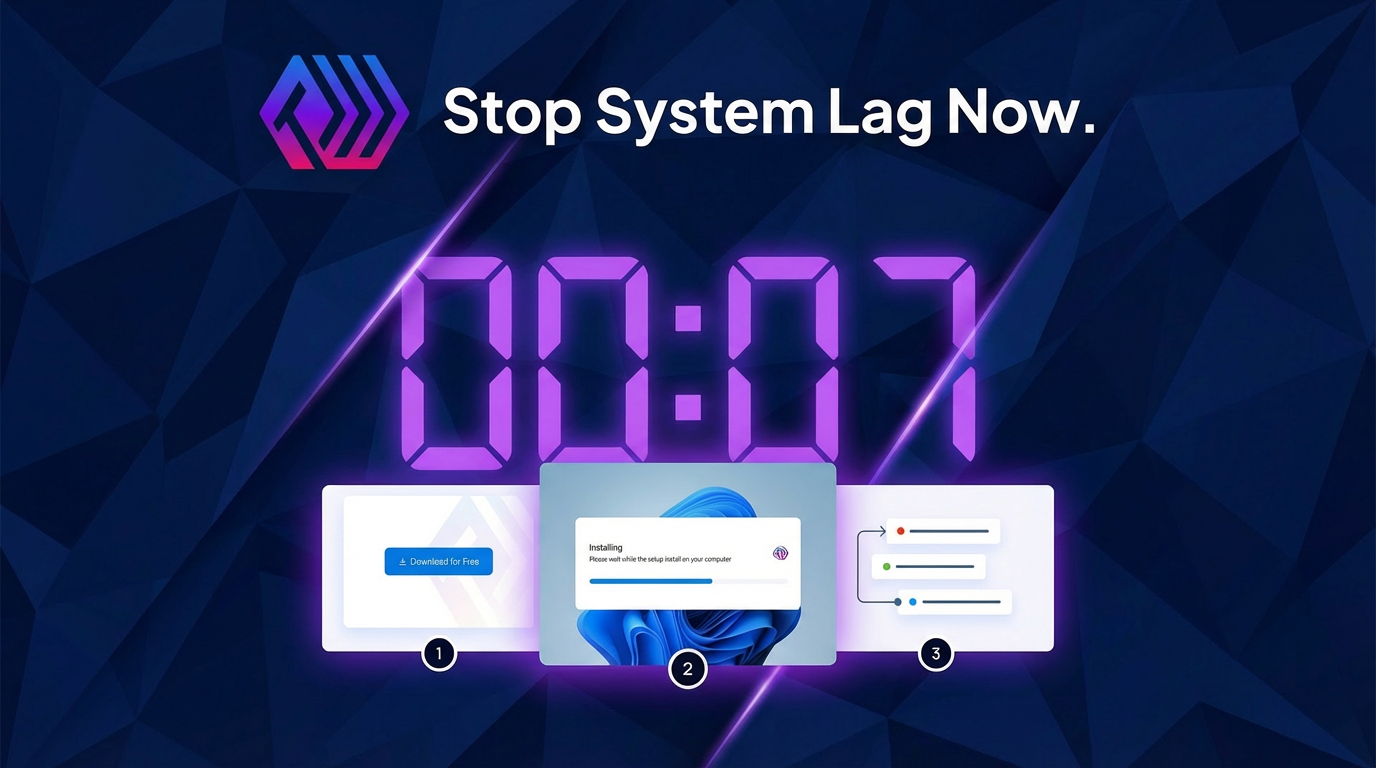
Fixing Startup Overload
Too many startup apps = slow system from the moment it turns on
How to fix:
- Open Task Manager (Ctrl + Shift + Esc)
- Go to the Startup tab
- Disable unnecessary app
Result:
- Faster boot time
- Lower memory usage
- Better performance from the start
Less clutter means more power for what matters.
Clearing Cache for Better Speed
- Cache files help speed things up temporarily
- But over time, they: File Storage, slow down system response
What to do:
- Use Disk Cleanup or Storage Settings
- Remove: Temporary files, System cache & Browser cache
Benefits:
Frees up space, Improves responsiveness & Reduces system lag
Advanced Control: Managing Your System Like a Pro
- Task Manager isn’t just for closing apps
You can:
Monitor: CPU usage, Memory usage & Disk activity
Adjust process priority: Give more power to important apps & Reduce priority of background apps
Why Manual Optimization Isn’t Enough
Looking after which programs start when your computer does, what programs are running, and how they’re all given importance…well, it’s a continuing job that needs your attention and really eats up your time.
And your system isn’t static. New applications get installed, things running in the background will begin again, and how much power those things use goes up and down.
So, dealing with startup applications, processes, and priorities by hand…requires both time and continual work. Systems are forever shifting: applications get installed, processes in the background are restarted, and the amount of system resources used changes.
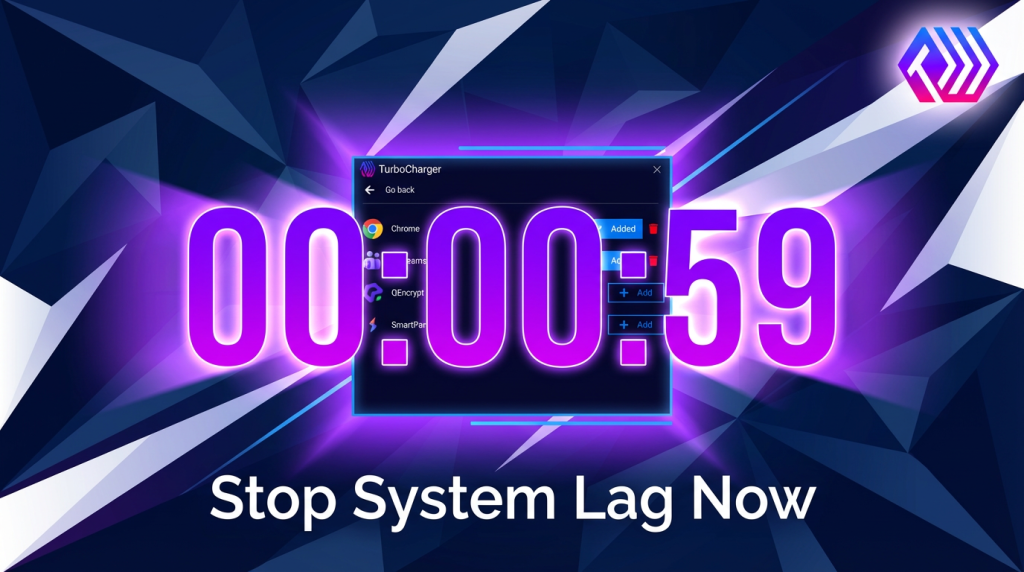
TurboCharger, and similar programs, keeps your computer running at its best by giving priority to the things you are using and quietly lessening what all the other, less important programs are doing. You don’t need to keep fiddling with settings; it does this optimization for you, by itself.
Combine Everything for Maximum Performance
To get your computer working as well as possible, you should consider getting more RAM if you require it, shut down programs that open automatically at the beginning (and you don’t actually use), frequently get rid of the files your computer has stored for quick access (the cache), keep an eye on how your system is doing, and manage how your computer uses things like processing power. Doing all of these things at once will give you a computer that’s quick, won’t break down, and reacts to what you do without delays.
Conclusion: Performance Is About Control, Not Just Hardware
Simply having quicker computer parts isn’t what makes a computer run at a better speed. It’s more about how well your computer uses the stuff it already includes. Most of the times things get slow for these reasons: resources aren’t being used in the best way, apps running in the background are doing more than they should, and the things you’re actively trying to do aren’t getting the power they need. TurboCharger will make sure your computer’s resources go to what you are doing, giving you a steady performance and stopping you from needing to endlessly change configurations.